Distributed inspection and policy enforcement embedded into the cloud network with centralized policy creation dramatically improves network security scalability, performance, operational simplicity, agility, and cost.
Santa Clara, Calif. – May 18, 2023 – Aviatrix, the pioneer of Secure Cloud Networking, today announced the immediate availability of its Distributed Cloud Firewall, redefining network security for cloud.
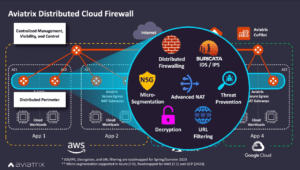
The Distributed Cloud Firewall distributes both inspection and policy enforcement into the natural path of application traffic, eliminating the need to redirect traffic to centralized firewalls or other network security services. A centralized programmable interface creates and pushes policies wherever required across any multicloud environment. Cloud aware policy creation is simpler and streamlined, leveraging dynamic cloud workload identity tags and attributes instead of static IP addresses, and abstracts how and where policies are enforced by programmatically configuring native cloud services where required. The Distributed Cloud Firewall dramatically improves network security scalability, operational simplicity, agility, and costs for any single or multicloud environment.
“This is more cloud native than native cloud firewalls. It’s a game changer for us,” said Jason Simpson, Vice President of Engineering at Choice Hotels. “Aviatrix has flipped the equation for network security in the cloud by distributing the inspection and enforcement throughout the cloud network to where the traffic naturally flows, rather than forcing traffic redirection to centralized inspection points. Aviatrix’s policy creation interface is novel and built for cloud, it abstracts multicloud differences and uses cloud native tags and attributes to define policies.”
Reinventing the Firewall for the Zero-Trust, Perimeterless Cloud
Modern cloud application workloads are containerized and ephemeral. They are designed for direct to internet and service mesh network connections. They require elastic scale and rely on native cloud platform-as-a-service (PaaS) services and API gateways, which break both traditional centralized and agent-based network security approaches in the cloud. Further, from a policy creation perspective, security teams can no longer define policies based on IP addresses because IP addresses constantly change in these dynamic application environments. Cloud infrastructure delivery must shift to the rapid release cycles embraced by applications teams, including DevSecOps automation and CI/CD pipelines. The primary reason enterprises migrated to cloud in the first place was to reduce traditional on-premises infrastructure deployment time from weeks/months to minutes/hours in the cloud. The traditional hardware appliance operational model, born for on-premises data center era architecture, is not feasible to meet the software-defined agility expectations of cloud.
What’s needed is a new approach – one with an architecture built from the ground up to support a cloud operational model and agile, perimeterless cloud environment – a distributed cloud firewall.
“Aviatrix’s Distributed Cloud Firewall is a new category of network security, built from the ground up for cloud,” said Scott Raynovich, Founder and Principal Analyst at Futuriom. “Applications drive infrastructure, and the applications in the cloud are driving the need to redefine how we implement network security. Today’s firewalls were designed for the on-prem perimeter, as a choke point to inspect traffic and deliver network security. In comparison, the cloud is perimeterless, and must therefore take a different approach for network security. The optimal way to achieve this is to distribute security by embedding it into the fabric of the entire cloud network, to do security everywhere.”
The Requirements to be a Distributed Cloud Firewall
A distributed cloud firewall is modern network security done right for cloud, delivering enterprises what they need to secure the cloud. A distributed cloud firewall has unique requirements:
- Distributed Enforcement Embedded into Natural Cloud Traffic Flow – It sees everything; it’s not bolted on. Inspection and policy enforcement is embedded into the native cloud infrastructure and natural application communication flows, so all traffic is seen, and traffic does not have to be redirected to centralized inspection points, eliminating bottlenecks and automatically scaling with application environments.
- Centralized Policy Creation – Cloud aware policy creation abstracts how and where policies are enforced using dynamic cloud native application workload identity tags and attributes, instead of static IP addresses, through a single, programmable interface that pushes policies where required across any multicloud environment.
- Cloud Operational Model – Enterprise owned and operated, it must deliver full visibility and control, elastic auto-scaling to match application requirements, be fully programmable with industry standard infrastructure as code automation, and included in DevSecOps CI/CD pipelines.
- Native Cloud Network and Security Orchestration Consistent Across Multicloud Environments – It supports native cloud APIs for both cloud network and cloud security orchestration to abstract underlying cloud infrastructure complexities, create consistency across cloud service providers, and avoid conflicts between networking and security configurations.
- Advanced Security Services Consolidation – More than basic firewalling, it supports microsegmentation, network isolation, automated threat detection and mitigation, anomaly detection, vulnerability scanning, cloud workload risk scoring, L7 decryption and inspection, full traffic visibility and audit reporting. Solutions must maintain a separation of networking and security duties through role-based access control, all embedded into native cloud infrastructure and operations.
“It’s time to reinvent network security, again,” said Steve Mullaney, President and CEO at Aviatrix. “Bolting on-prem firewalls onto a cloud network and trying to steer traffic to them is not effective for cloud, it’s just not how the cloud operates. The cloud is perimeterless, agile, dynamic, and scale-out by design. Network security must follow – it must be distributed and embedded into the network to deliver a true zero-trust, agile environment. Aviatrix’s Distributed Cloud Firewall is going to dramatically change the cloud security game for our customers and save them a lot of money in the process.”
Steve Mullaney will host Jason Simpson, VP of Engineering at Choice Hotels, for a keynote fireside chat at ONUG Spring 2023 in Dallas, Texas. Choice Hotels, with nearly 7,500 hotels in more than 40 countries, is deploying Aviatrix in its modern cloud infrastructure to increase enterprise-grade agility, resiliency, and security.
To learn more about Aviatrix’s Distributed Cloud Firewall, visit: https://aviatrix.com/distributed-cloud-firewall.
About Aviatrix
Trusted by more than 500 of the world’s most innovative companies, Aviatrix empowers businesses to accelerate innovation, improve security, minimize downtime, and gain control of IT costs in the cloud. Aviatrix delivers an enterprise-grade secure cloud network, backbone, and edge for business-critical applications by creating a simplified and consistent networking and security architecture in and across cloud service providers. Combined with the Aviatrix Certified Engineer (ACE) Program, the industry’s first and only multicloud networking and security certification, Aviatrix helps businesses to achieve their digital transformation goals. Learn more at www.aviatrix.com.

